Key Takeaways
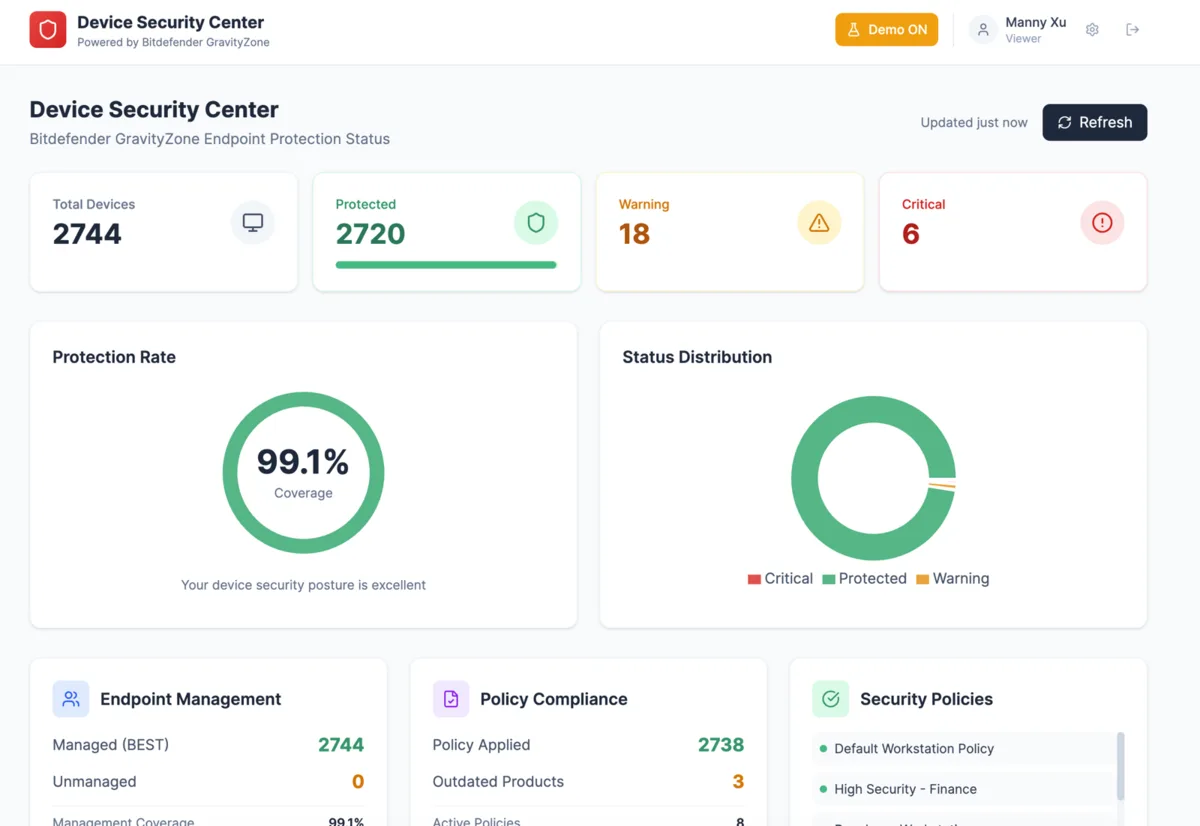
- Callnovo protects 2,500+ agent endpoints across the Philippines, Colombia, and other global sites with Bitdefender enterprise security — Every device that touches client data runs managed endpoint protection with real-time monitoring.
- We built a custom management webapp on top of Bitdefender’s API because off-the-shelf tools don’t fit distributed BPO operations — Each site manager can monitor, patch, and enforce policies for their own endpoints without accessing other sites’ data — true operational isolation.
- For clients with strict compliance requirements (HIPAA, PCI-DSS, government contracts), we offer Bitdefender EDR as an add-on — Extended Detection and Response gives real-time threat hunting, forensic investigation, and incident response capabilities beyond standard endpoint protection.
- Security isn’t a checkbox for us — it’s an engineering problem we invest in continuously — Building internal tooling on security vendor APIs is the kind of work that doesn’t show up in sales decks but defines whether a BPO can actually protect client data at scale.
The Problem Nobody Talks About in BPO Security
Here’s what most BPO companies won’t tell you: managing endpoint security across a distributed, multinational workforce is genuinely hard. Not “hard” in the way people say it in marketing copy. Hard in the way that makes engineers lose sleep.
At Callnovo, we operate from delivery centers and remote setups across the Philippines, Colombia, Mexico, Pakistan, and several other countries. Over 2,500 agents. Hundreds of workstations, laptops, and thin clients. Multiple operating systems. Wildly different network environments. Regulatory requirements that vary by country and by client. And every single one of those endpoints is a potential attack surface.
Most BPOs handle this by buying an enterprise security license, installing the agent on every machine, and calling it done. That works if you’re a single-site operation. It breaks completely when you’re running distributed sites with local management teams who need autonomy.
Why We Chose Bitdefender
We evaluated five endpoint security platforms before landing on Bitdefender GravityZone. The decision came down to three factors:
Detection quality. Bitdefender consistently ranks at the top of independent testing — AV-TEST, AV-Comparatives, MITRE ATT&CK evaluations. In our industry, where agents handle PII, financial data, and sometimes PHI, a missed detection isn’t just an IT incident. It’s a client relationship ending.
API-first architecture. This was the dealbreaker. We needed a security platform that exposed a comprehensive API so we could build management tooling that matched our operational model. Most enterprise security products are designed around a single admin console for a single organization. That doesn’t work for us. More on this below.
Lightweight agent footprint. Our agents in some regions work on modest hardware. A security agent that consumes 500MB of RAM and pegs the CPU during scans makes the workstation unusable. Bitdefender’s agent is lean enough that our agents don’t even notice it’s running — which is exactly how endpoint security should work.
What We Built: Site-Isolated Endpoint Management
Here’s where it gets interesting — and where we differ from most BPOs.
Bitdefender GravityZone comes with a solid cloud console. It works well for a centralized IT team managing one organization. But our operational model is different. Each Callnovo delivery site has a local operations manager who is responsible for their site’s security posture. The site manager in Manila needs to see their endpoints, enforce their policies, and respond to their alerts — without seeing or affecting endpoints in Bogotá or Manila.
Off-the-shelf, no enterprise security product handles this well. Multi-tenancy in security platforms is designed for MSPs managing separate customers, not for a single organization managing separate sites with isolated visibility.
So we built our own.
Using Bitdefender’s GravityZone API, we developed an internal webapp that gives each site manager a scoped, isolated view of their endpoints. Here’s what it does:
Site-scoped dashboards. Each site manager logs in and sees only their endpoints — device health, protection status, last scan times, pending updates, quarantined threats. No access to other sites. No ability to modify global policies. Clean isolation.
Automated compliance checks. The webapp runs continuous checks against our internal security baseline: Is the Bitdefender agent running? Is it up to date? Is the firewall enabled? Is the disk encrypted? Is the device checking in regularly? Any endpoint that falls out of compliance gets flagged immediately, and the site manager gets an alert.
Patch and policy enforcement. Site managers can push Bitdefender policy updates to their endpoints — scan schedules, exclusion rules, network protection settings — without needing access to the central GravityZone console. The webapp validates that site-level policies don’t conflict with our global security baseline before applying them.
Incident response workflow. When a threat is detected, the webapp creates a structured incident record: what was detected, on which endpoint, what action was taken (quarantine, block, clean), and whether it requires escalation. The global security team sees all incidents across all sites, but site managers only see their own.
What This Looks Like in Practice
A typical day in our security operations:
Morning (Asia hours). Site managers in the Philippines and other Asian sites check their dashboards. A workstation in one site shows a Bitdefender agent that hasn’t checked in for 18 hours — the machine was powered off for maintenance. The manager confirms, marks it resolved. Another endpoint flagged a PUP (potentially unwanted program) that an agent accidentally downloaded. Bitdefender quarantined it automatically. The site manager reviews the quarantine log, confirms it’s clean, and logs the incident.
Afternoon (Americas hours). The Colombia site is onboarding 15 new agents for a client ramp-up. The site manager uses the webapp to verify that every new workstation has the Bitdefender agent installed, policies applied, and first full scan completed — all before the agents handle a single client interaction. Three machines fail the compliance check because disk encryption hasn’t finished. They’re held from production until encryption completes.
Continuous. The global security dashboard shows all sites green. No active threats. 99.7% agent check-in rate across all endpoints. The 0.3% are machines in scheduled maintenance windows. The system is working the way it should: quietly, continuously, and without drama.
Bitdefender EDR: For Clients Who Need More
Standard endpoint protection — antivirus, firewall, web filtering — is sufficient for most engagements. But some of our clients operate in regulated industries where “sufficient” doesn’t meet compliance requirements. Healthcare companies under HIPAA. Financial services under PCI-DSS. Government contractors. Visa processing centers handling embassy-grade sensitive documents.
For these clients, we offer Bitdefender Endpoint Detection and Response (EDR) as an add-on to our service.
EDR goes beyond prevention. It provides:
Real-time threat hunting. Continuous monitoring of endpoint behavior — process execution, file modifications, network connections, registry changes — with AI-driven anomaly detection. If something behaves like a threat even if it hasn’t been seen before, EDR catches it.
Forensic investigation. When an incident occurs, EDR provides a complete timeline: how the threat entered, what it touched, how it moved laterally, and what data it accessed. This is critical for compliance reporting — regulators don’t just want to know that you stopped a threat. They want to know exactly what happened.
Automated response. EDR can isolate a compromised endpoint from the network in seconds — before a human even sees the alert. For BPO environments where agents are handling live customer data, the speed of containment is everything.
We don’t upsell EDR to clients who don’t need it. But for engagements where a security incident could mean regulatory penalties, breach notifications, or contract termination, the additional layer of visibility and response capability is worth every penny.
Why This Matters for Our Clients
We don’t write blog posts about our security infrastructure to impress people. We write them because our clients — and their compliance teams, and their auditors — need to know that their data is protected by more than a checkbox on an RFP response.
When a client asks “how do you handle endpoint security?”, we don’t say “we use antivirus.” We show them:
- The specific platform we use and why
- The custom tooling we built to manage it across distributed sites
- The isolation model that prevents cross-site exposure
- The compliance automation that catches gaps before auditors do
- The EDR capability available for high-security engagements
This is what security looks like when it’s treated as an engineering discipline, not a procurement line item.
We’re a BPO company that builds internal developer tools. That might seem unusual. But when you’re responsible for protecting sensitive data across 2,500+ endpoints in 6+ countries, “usual” isn’t good enough.
What’s Next
We’re currently expanding the webapp with automated remediation workflows — the ability to not just detect non-compliant endpoints but automatically bring them back into compliance without manual intervention. We’re also building integration between our Bitdefender management layer and HeroDash, so that security posture becomes visible alongside operational metrics. If an agent’s workstation is compromised, their active tickets should be flagged for review.
Security isn’t a destination. It’s a practice. We’ll keep investing in it because our clients’ data demands nothing less.