Key Takeaways
- A client’s payment to Callnovo failed because the bank details had been changed — by a fraudulent email that looked exactly like ours. The email appeared to come from our accounts receivable, was CC’d to all relevant parties, and requested a routine bank account update.
- Our immediate investigation found zero evidence of a breach on our side — MFA was enabled, sent email logs were clean, and no unauthorized access was detected. The compromise was traced to the client’s environment.
- We reported the fraudulent bank account (Truist, opened in Atlanta) by calling the bank and physically visiting a branch. When financial fraud is in play, digital-only reporting isn’t enough.
- We now require video call verification for all bank account changes — no exceptions. This one policy change eliminates the entire attack vector. We recommend every business working with international vendors adopt the same practice.
The Email That Almost Worked
Last month, a long-standing client tried to remit their monthly service payment to us. It failed. The bank rejected the transfer because the account details didn’t match.
When they contacted us to sort it out, they forwarded an email they’d received — one that had been forwarded internally by one of their own employees. The original email appeared to come from our accounts receivable department. It requested a change to our bank account details for future payments. The email was well-formatted, used correct terminology, and CC’d all the relevant people on both sides.
At first glance, it looked completely legitimate. Even to us.
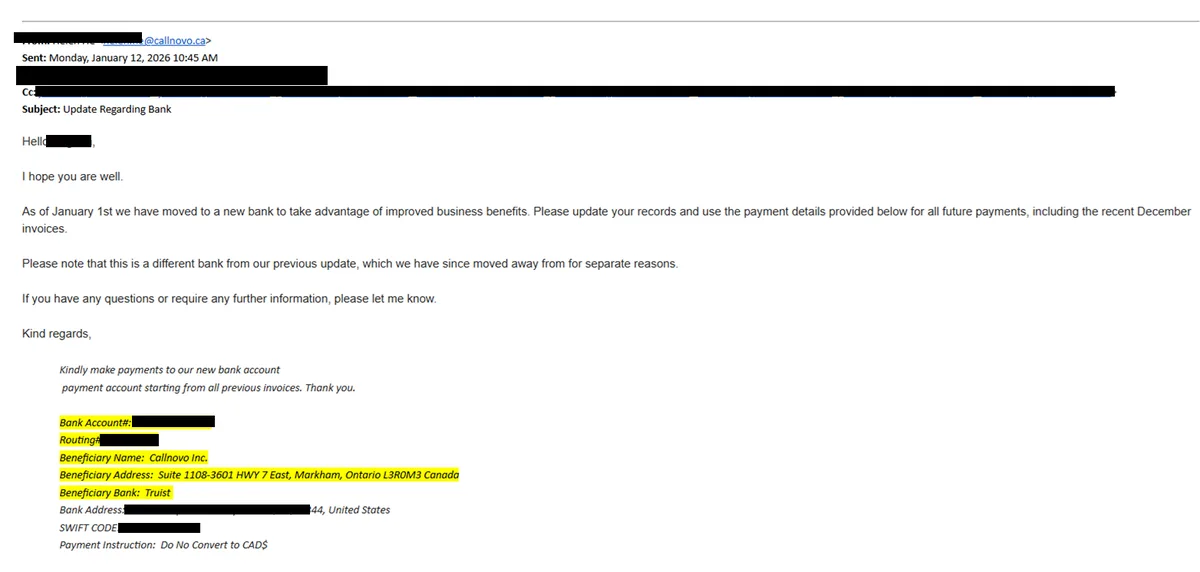
The actual fraudulent email our client received. Names, account numbers, and other identifying details have been redacted.
The new bank details pointed to a Truist account opened in Atlanta. We don’t bank with Truist. We don’t have any accounts in Atlanta. Someone had created a fraudulent bank account and impersonated us to redirect our client’s payment into it.
The First 24 Hours: “Did We Get Breached?”
When we saw that email, the first question was the obvious one: had our email system been compromised?
Here’s what we did within the first few hours:
Email System Audit
Checked all sent mail logs for our accounts receivable address. No record of the fraudulent email ever being sent from our systems. Zero.MFA Verification
Confirmed that multi-factor authentication was active on all email accounts, including accounts receivable. No MFA bypass attempts detected.Access Log Review
Reviewed login history across all email accounts for unusual IP addresses, devices, or geolocations. Nothing abnormal.Bank Reporting
Called the bank (Truist) to report the fraudulent account. Then physically walked into a local branch to file a formal fraud report in person.The email audit was the critical piece. If that fraudulent email had actually been sent from our mail servers, we’d be dealing with a breach — and that would mean incident response, client notifications, the whole protocol. But our logs were clean. The email wasn’t sent from us. It was crafted to look like it was sent from us.
What Actually Happened
After our client conducted their own internal investigation, the picture became clearer. The compromise originated outside our systems. The attacker had enough context about our business relationship — names, roles, payment cadence, email formatting — to construct a convincing impersonation.
This is the anatomy of a BEC attack:
1. Reconnaissance. The attacker identified a real vendor-client relationship (us and our client) and gathered enough detail to make the impersonation credible — names, titles, email formats, the fact that regular payments were being made.
2. Impersonation. They crafted an email that mimicked our accounts receivable communication style. Right domain structure, right CC list, right tone. The kind of email that, in a busy accounts payable department processing dozens of invoices, doesn’t raise a flag.
3. The ask. A simple, routine-sounding request: “We’ve updated our banking details. Please use the following account for future payments.” No urgency. No pressure. Just a matter-of-fact update — which is exactly what makes it dangerous.
4. The redirect. The new account was a Truist account opened in Atlanta. Legitimate-looking bank, legitimate-looking location. Nothing about it screamed “fraud” at first glance.
The only reason it failed? The payment was rejected by the receiving bank due to a mismatch in account details. If those details had matched — if the attacker had been slightly more careful — the payment would have gone through.
What We Did About the Fraudulent Account
Digital reporting alone isn’t sufficient when financial fraud is involved. Here’s what we did:
Called Truist’s fraud department directly. We reported the account number, explained the BEC attempt, and requested the account be flagged for investigation.
Physically visited a bank branch. We walked into a branch and filed a formal fraud report with a banker in person. This creates a paper trail that’s harder to ignore than an online form. When someone is sitting across from you explaining that a fraudulent account was opened at their institution, it gets attention.
Documented everything. Full timeline, email headers, account details, communications with our client — all preserved for potential law enforcement involvement.
The Policy Change: Video Verification for All Bank Account Changes
This incident exposed a gap that exists in almost every B2B relationship: there is no standard verification protocol for bank account changes.
Think about it. A company emails you saying “here are our new bank details.” What do you do? Most companies check if the email looks legitimate, maybe call a phone number listed in the email (which the attacker controls), and process the change. That’s it.
We’ve now implemented a simple, unbreakable rule:
All changes to bank account details — ours or our clients’ — must be verified via live video call with a known contact at the other company.
Not email. Not phone (phone numbers can be spoofed). A live video call where you can see the person you’ve been working with, confirm their identity, and verbally confirm the banking change.
This is not a high-tech solution. It’s a human solution. And that’s precisely why it works against an attack that exploits human trust. You can spoof an email. You can spoof a phone number. You cannot spoof a live video call with someone your team already knows.
We now proactively remind every client of this policy at the start of each engagement and during quarterly business reviews. If you receive any communication requesting a change to our banking details, do not process it until you’ve verified it on a video call with your Callnovo account manager.
Lessons for Every Business Working with International Vendors
This incident reinforced several principles that apply to any company managing B2B payments:
1. Never process a bank account change based solely on an email. No matter how legitimate it looks. No matter who it’s CC’d to. No matter how routine the request sounds. Always verify through a separate, authenticated channel — ideally video.
2. “We have MFA” is necessary but not sufficient. Our MFA was active and working. It protected our systems. But BEC doesn’t need to breach your systems — it just needs to impersonate them convincingly. MFA protects against account takeover. It doesn’t protect against impersonation.
3. Report fraud physically, not just digitally. When we walked into a bank branch to report the fraudulent account, the response was materially different from what we’d gotten over the phone. In-person reporting creates accountability and urgency that digital forms don’t.
4. Your vendor’s security is only as strong as your own. We had clean systems, MFA, endpoint security (Bitdefender across 2,500+ devices), and audited access logs. The attack still almost worked because the entry point was outside our perimeter. Supply chain security is a shared responsibility.
5. Assume every “routine” financial communication is a potential attack. The most dangerous BEC emails are the ones that don’t feel urgent. They feel normal. That normalcy is the weapon.
Moving Forward
We’re sharing this story because transparency about security incidents — even ones that were caught before causing damage — makes the entire ecosystem safer. Every business that reads this and implements video verification for banking changes is one fewer potential victim.
If you’re a current Callnovo client: you’ve already been briefed on our video verification policy. If you ever receive an email requesting a change to our banking details, do not act on it. Call your account manager. Start a video call. Verify.
If you’re evaluating BPO partners: ask them what happens when someone emails a request to change bank account details. If the answer is anything other than “we verify via a separate authenticated channel,” keep looking.
Security isn’t just about the technology you deploy. It’s about the processes you build around it.